HIBP vs CyberPeople compared: breach databases, infostealer detection, k-anonymity.
Have I Been Pwned vs CyberPeople Breach Check: What's the Difference?
If you have ever searched "has my email been hacked?", you have almost certainly landed on Have I Been Pwned (HIBP) — the industry-standard breach notification service created by Troy Hunt. It is a genuinely excellent tool, and its contribution to public cybersecurity awareness is hard to overstate.
But the threat landscape has changed. Data breaches are no longer the only way your credentials end up in criminal hands. Infostealer malware — programs like RedLine, Raccoon, and Vidar — silently harvest passwords, cookies, and autofill data directly from infected devices. These logs are traded on Telegram channels and dark web marketplaces every single day, and they do not show up in traditional breach databases.
That is the gap CyberPeople's "Am I Breached?" tool was built to close. It checks both breach databases and infostealer intelligence in a single lookup.
In this article we compare the two services side by side — respectfully, transparently, and with the goal of helping you choose the right tool for your situation.
Quick Comparison Table
| Feature | Have I Been Pwned | CyberPeople Breach Check |
|---|---|---|
| Price | Free (premium API plans available) | Free |
| Data breach check | Yes — 970+ breached sites, 17.5 B+ accounts | Yes — via XposedOrNot (10.7 B+ records) |
| Infostealer / malware check | No | Yes — via HudsonRock Cavalier (30 M+ compromised machines) |
| Password check | Yes — k-anonymity model | Yes — k-anonymity model (SHA-1, browser-side hashing) |
| Languages | English | English, Ukrainian |
| Registration required | No (optional for notifications) | No |
| API data source | Proprietary HIBP database | XposedOrNot (breaches) + HudsonRock Cavalier (infostealers) |
| Cyber Score rating | No | Yes — 0-100 score with risk level |

What Exactly Are Infostealers — and Why Should You Care?
An infostealer is a type of malware specifically designed to extract sensitive data from an infected computer. Unlike a data breach, where a company's server is compromised, an infostealer targets your device directly.
Here is what a typical infostealer grabs in seconds:
- All saved passwords from every browser on the machine
- Active session cookies (allowing attackers to bypass two-factor authentication entirely)
- Credit card numbers stored in browser autofill
- Cryptocurrency wallet files
- Desktop files, screenshots, and system information
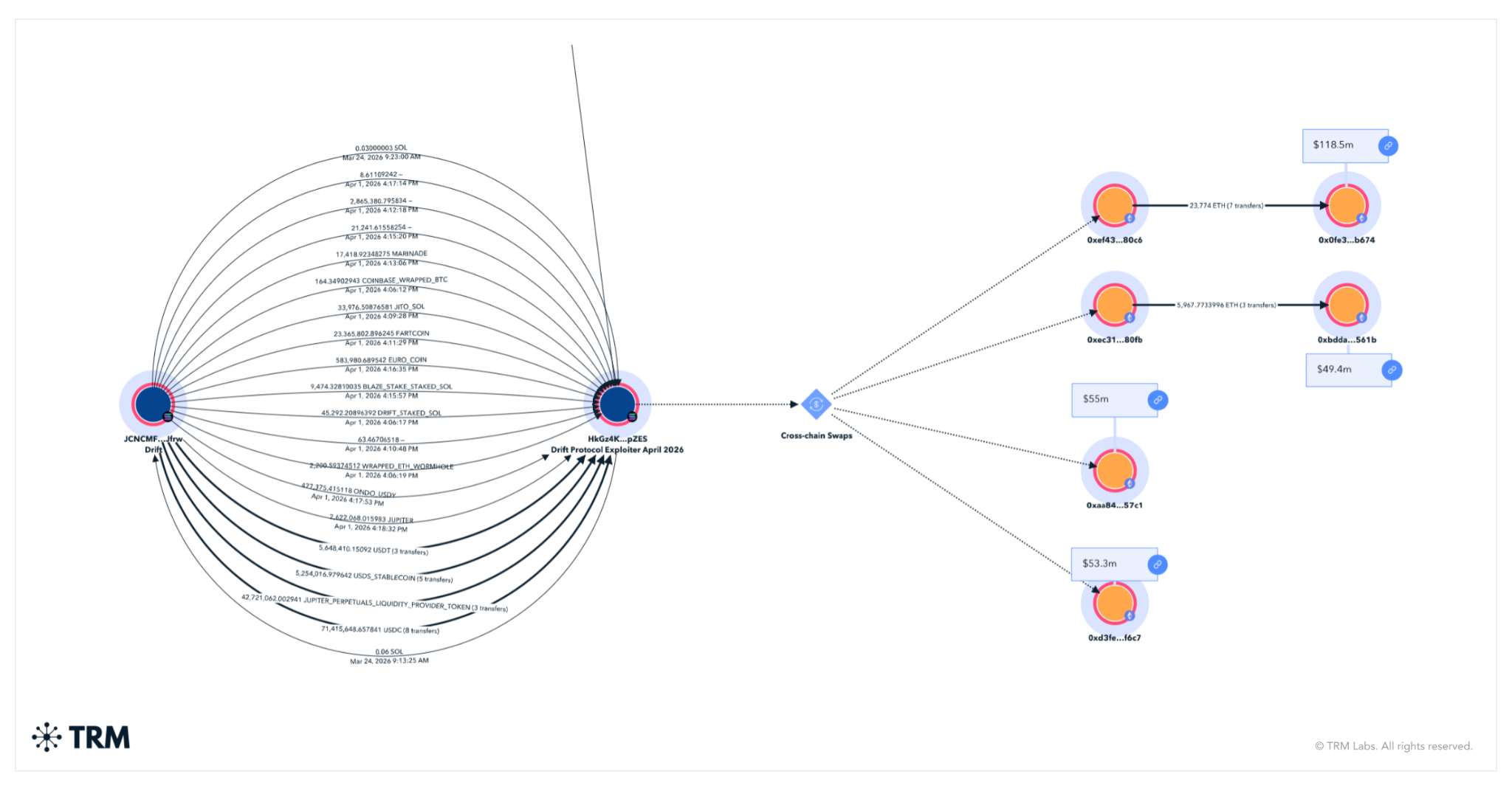
The stolen data — called a "stealer log" — is then sold or shared on underground markets. Hudson Rock's Cavalier platform tracks over 30 million compromised machines from global infostealer campaigns, and the database grows daily.
The critical point: stealer logs are fundamentally different from breach data. A breach means a company lost your data. A stealer log means your personal device was infected, and every credential on it — across dozens or hundreds of services — is now in criminal hands. One infection can expose your entire digital life.
HIBP does not cover this category. CyberPeople does.

How Password Checking Works: k-Anonymity Explained
Both HIBP and CyberPeople allow you to check whether a specific password has appeared in known leaks. Both use the same privacy-preserving technique: k-anonymity.
Here is how it works, step by step:
- Your password is hashed locally. The tool converts your password into a SHA-1 hash entirely inside your browser. The plaintext password never leaves your device.
- Only a prefix is sent. The first 5 characters of the hash are sent to the server. For example, if your password hashes to
F3BBB...D21D, onlyF3BBBis transmitted. - The server returns a bucket of matches. The API responds with every hash suffix in its database that shares those 5 characters — typically hundreds of entries.
- Your browser checks locally. The tool compares your full hash against the returned list on your device. The server never knows which specific hash you were looking for.
This approach, first described by Cloudflare and Troy Hunt in 2018, ensures that even a compromised API server cannot determine which password you queried. It is elegant, effective, and both platforms implement it correctly.

Where HIBP Excels
Credit where it is due. Have I Been Pwned has several clear strengths:
- The largest proprietary breach database in the world — 970+ breached sites, 17.5 billion compromised accounts, and growing.
- Direct partnerships with law enforcement — FBI and other agencies feed seized breach data directly into HIBP.
- "Notify Me" alerts — automated email notifications when your address appears in a future breach.
- Domain-wide search — organizations can monitor all email addresses on their domain.
- Mature, battle-tested API — widely integrated into password managers (1Password, Bitwarden) and enterprise tools.
- Trusted brand — over a decade of consistent, transparent operation.
For pure breach monitoring, HIBP remains the gold standard.
Where CyberPeople Adds Value
CyberPeople's "Am I Breached?" tool was not built to replace HIBP. It was built to cover the blind spot that HIBP does not address:
- Infostealer detection — powered by HudsonRock Cavalier, the tool checks if your email appears in stealer logs from malware like RedLine, Raccoon, Vidar, and others. This is the single biggest differentiator.
- Combined results in one view — breach data (via XposedOrNot) and stealer log data are displayed together, giving you a complete exposure picture.
- Cyber Score (0-100) — a simple, visual rating that categorizes your risk as Secure, At Risk, or Compromised.
- Ukrainian language support — serving the Ukrainian cybersecurity community in their native language.
- No registration required — instant results, no account needed.
Breach Data vs. Stealer Log Data: A Key Distinction
Understanding the difference between these two data types is essential:
Breach data originates from a compromised company. A server is hacked, a database is dumped, and the records (emails, hashed or plaintext passwords, personal details) eventually surface on the internet. The data is typically from one service at a time.
Stealer log data originates from an infected personal device. Malware runs on someone's computer and harvests every credential the browser has saved — often spanning 50 to 200 different services in a single log. It also includes session cookies, which can bypass MFA.
If your email appears in a breach database, you should change that specific password. If your email appears in a stealer log, you should change every password on every service you have ever used from that device, revoke active sessions, and scan the machine for malware.
The response is fundamentally different. That is why knowing which type of exposure you are dealing with matters.
When to Use Which
Our recommendation is straightforward: use both.
- Use Have I Been Pwned for its unmatched breach database, domain monitoring, and notification service. If you want to know whether a specific company leak includes your email, HIBP is the definitive source.
- Use CyberPeople Breach Check for a complete picture that includes infostealer infections. If you want to know whether your device was compromised by malware and your credentials are circulating in stealer logs — this is the tool that answers that question.
Together, the two tools cover both major vectors of credential exposure: server-side breaches and client-side infections.

Try It Yourself
Check your email in under 30 seconds — no registration, no cost, no data stored.
Check your exposure now on CyberPeople
If the results show infostealer activity, take it seriously: change all passwords saved in the affected browser, revoke active sessions, and run a full malware scan on the device.
CyberPeople is a Ukrainian cybersecurity platform providing threat intelligence, community resources, and free security tools. The "Am I Breached?" tool combines data from XposedOrNot and HudsonRock Cavalier to deliver comprehensive exposure checks.




Comments
No comments yet. Be the first to comment!
Leave a Reply
Your email address will not be published.