McAfee uncovers NoVoice rootkit in 50+ Google Play apps. Uses steganography, 22 exploits, hijacks WhatsApp. Factory reset won't save you.
More than 2.3 million Android devices have been compromised by a sophisticated rootkit that hid inside 50+ legitimate-looking Google Play apps, exploits 22 known vulnerabilities to gain kernel-level access, uses steganography to conceal its payload inside ordinary PNG images, and persists through factory resets. Its primary mission: silently cloning victims' WhatsApp sessions and handing them to attackers.
McAfee's Mobile Research Team, operating as part of Google's App Defense Alliance, uncovered the campaign they track as Operation NoVoice -- one of the most technically advanced Android malware operations discovered in recent years. The affected apps have since been removed from Google Play, but the damage to millions of devices running outdated Android versions cannot be undone with a simple reset.
Here is everything defenders and users need to know.
How It Started: 50+ Apps, Zero Suspicion
The NoVoice campaign was distributed through more than 50 applications on Google Play, all disguised as everyday utility software: phone cleaners, image gallery tools, and casual games. These apps required no suspicious permissions and delivered the functionality they advertised. Users had no reason to doubt them.
Collectively, the malicious apps accumulated at least 2.3 million downloads before McAfee reported them and Google removed them from the store. The apps are no longer available for download, but devices that installed them and lacked adequate security patches remain compromised.
What made NoVoice particularly dangerous was its patience. The apps functioned normally on the surface while silently profiling each device and reaching out to command-and-control (C2) infrastructure in the background, waiting for instructions to begin the real attack.
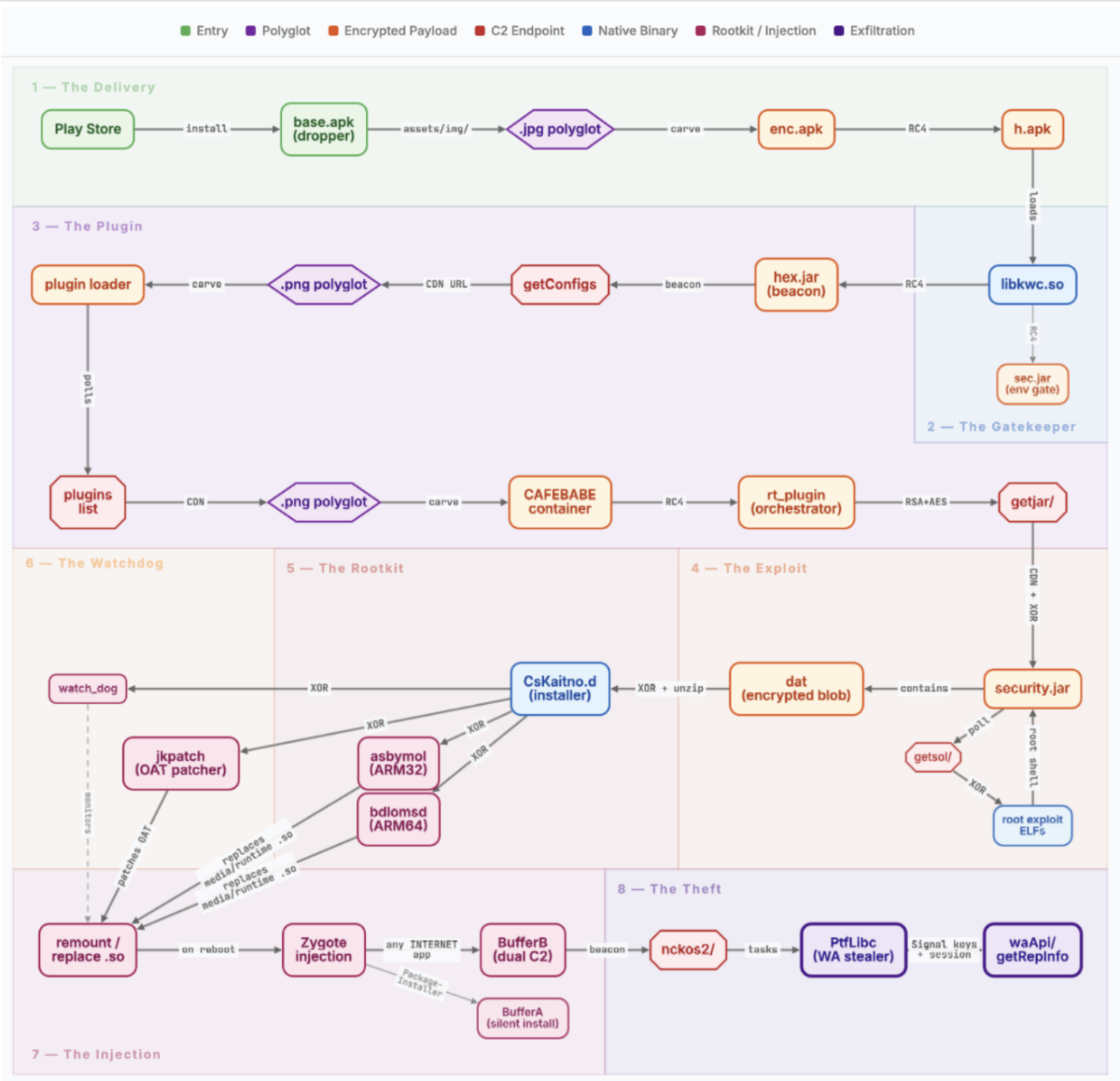
The Steganography Trick: Malware Hidden Inside Images
NoVoice employed an elegant concealment technique that allowed its malicious payload to pass undetected through Google Play's security scanning and most third-party antivirus engines.
The attackers embedded an encrypted payload (enc.apk) inside an ordinary PNG image file using steganography. The malicious data was appended after the PNG file's IEND marker -- the standard end-of-file indicator for PNG images -- and prefixed with the magic value CAFEBABE. Because image viewers and standard security scanners stop reading a PNG file at the IEND marker, the hidden payload was effectively invisible to automated analysis.
Once on the device, the malware extracted this concealed payload as h.apk, loaded it directly into system memory, and immediately wiped all intermediate files from disk to eliminate forensic traces.
The threat actors further obfuscated their work by hiding malicious components inside a package named com.facebook.utils, mixing their code with legitimate Facebook SDK classes.
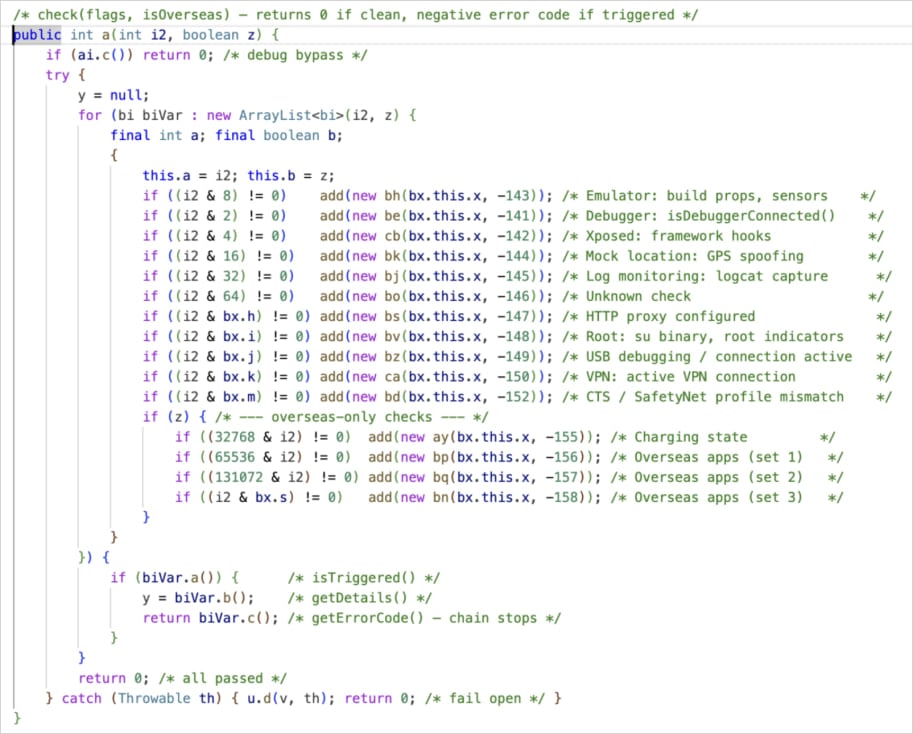
15 Checks Before Attacking: Anti-Analysis Defenses
Before deploying any exploit, NoVoice ran an extensive series of 15 verification checks designed to ensure it was operating on a real victim device rather than a security researcher's analysis environment. These checks scanned for:
- Emulator environments commonly used by malware analysts
- Active debuggers attached to the process
- VPN and proxy connections that might indicate traffic interception
- Rooting hooks from frameworks like Magisk or Xposed
- GPS geofencing to exclude specific geographic regions
Notably, the malware was configured to avoid infecting devices physically located in Beijing and Shenzhen, China.
22 Exploits, One Goal: Root Access
The core of NoVoice's capability rested on an arsenal of 22 distinct exploits identified by McAfee researchers. All of these exploits targeted known Android vulnerabilities that were patched between 2016 and 2021.
The malware's C2 server played an active role in exploit selection. After profiling each target device, the server selected and delivered the optimal exploit chain for that specific hardware and software combination.
A Three-Stage Kernel Attack
McAfee's deep analysis of one exploit chain revealed a sophisticated three-stage kernel attack:
- Stage 1 -- Kernel Read Access: An IPv6 use-after-free vulnerability was exploited to gain the ability to read arbitrary kernel memory.
- Stage 2 -- Kernel Read/Write Access: A Mali GPU driver vulnerability was leveraged to escalate from read-only to full read/write access to kernel memory.
- Stage 3 -- Full Compromise: With unrestricted kernel memory access, the exploit patched process credentials and disabled SELinux protections entirely.
The Unkillable Rootkit: How NoVoice Achieves Persistence
Once root access was obtained, the rootkit installer component -- identified by researchers as CsKaitno.d -- was decrypted from an embedded resource and written to disk.
System Library Replacement
The rootkit replaced critical Android system libraries, specifically libandroid_runtime.so and libmedia_jni.so, with malicious wrapper binaries. Because libandroid_runtime.so is loaded by every Android application at launch, this single modification meant that every app on the device ran attacker code the moment it started.
Recovery Scripts and Crash Handler Hijacking
NoVoice installed recovery scripts on the system partition and replaced the Android system crash handler with a rootkit loader.
Fallback Payloads
Additional malicious payloads were stored on the system partition -- a partition that is not touched during a standard factory reset. This is the critical reason why factory reset cannot remove NoVoice.
Watchdog Daemon
A persistent watchdog daemon ran every 60 seconds, checking the rootkit's integrity across all persistence layers.
The Silent Audio Trick
The campaign's name, "NoVoice," derives from a specific technical detail: the malware embedded a silent audio resource file (R.raw.novioce -- note the intentional misspelling) that was played continuously to keep an Android foreground service alive.
WhatsApp Session Hijacking: The Real Payload
While the NoVoice framework was architecturally designed to accept and execute any task delivered by the C2 server, the only confirmed theft payload recovered by McAfee researchers was focused on a single target: WhatsApp.

When WhatsApp was launched on an infected device, the rootkit's injected code detected the WhatsApp launch and extracted:
- Encryption databases containing message history
- Signal protocol keys used for end-to-end encryption
- Account identifiers including the victim's phone number
- Google Drive backup details for cloud-stored message archives
This data was exfiltrated to the C2 server, enabling attackers to clone the victim's WhatsApp session on an attacker-controlled device.
Connection to the Triada Malware Family
Security researchers have identified strong technical similarities between NoVoice and the notorious Triada malware family. Several specific indicators link the two:
- NoVoice sets the system property os.config.ppgl.status to mark a device as compromised.
- Both NoVoice and Triada persist by replacing libandroid_runtime.so and hooking system functions.
- The overall persistence architecture follows patterns established by earlier Triada variants.
Implications for Ukrainian Users
This threat carries particular significance for Ukrainian users.
Older Devices and the Vulnerability Window
Ukraine's smartphone market is heavily skewed toward budget and mid-range Android devices. Over 15% of Ukrainian Android users remain on Android 10 or older versions. The economic pressures of the ongoing war have further extended device lifecycles.
Wartime OPSEC and WhatsApp Session Cloning
WhatsApp is used in Ukraine for personal communication and, in some cases, for coordination that touches on sensitive wartime matters. The ability to silently clone a WhatsApp session represents a serious operational security threat.
Messaging App Considerations
Ukrainian users handling sensitive communications should evaluate their messaging platform choices carefully. Signal offers stronger architectural protections against session cloning.
Known Indicators of Compromise
Technical Indicators:
- Presence of CsKaitno.d binary on the device
- Modified libandroid_runtime.so or libmedia_jni.so system libraries
- System property os.config.ppgl.status set on the device
- Package containing com.facebook.utils with code not matching legitimate Facebook SDK
- Silent audio resource file R.raw.novioce in installed applications
How to Check If You Are Affected
Step 1: Check Your Security Patch Level
Open Settings > About Phone > Android Security Patch Level. If your security patch level is May 2021 or later, your device is not vulnerable.
Step 2: Review Installed Apps
If your patch level predates May 2021, review your installed applications.
Step 3: Check for Signs of Compromise
Look for behavioral indicators: unexplained battery drain, WhatsApp session anomalies, spontaneous reboots.
Step 4: If Compromised -- Firmware Reflash Is Required
A factory reset will not remove NoVoice. The only reliable remediation is a complete firmware reflash.
Protection Recommendations
For Individual Users
- Keep your device updated.
- Enable Google Play Protect.
- Be skeptical of utility apps.
- Verify app publishers.
- Consider device upgrade.
For Organizations
- Implement Mobile Device Management (MDM).
- Enforce app whitelisting.
- Conduct device compliance checks.
- Establish secure communication protocols.
- Plan for compromised device scenarios.
This analysis is based on research published by McAfee's Mobile Research Team.
Sources:




Comments
No comments yet. Be the first to comment!
Leave a Reply
Your email address will not be published.