Threat actor UAC-0255 impersonated CERT-UA to distribute AGEWHEEZE RAT across 1M Ukrainian mailboxes. Go-based malware targets state, medical, financial, and security organizations.
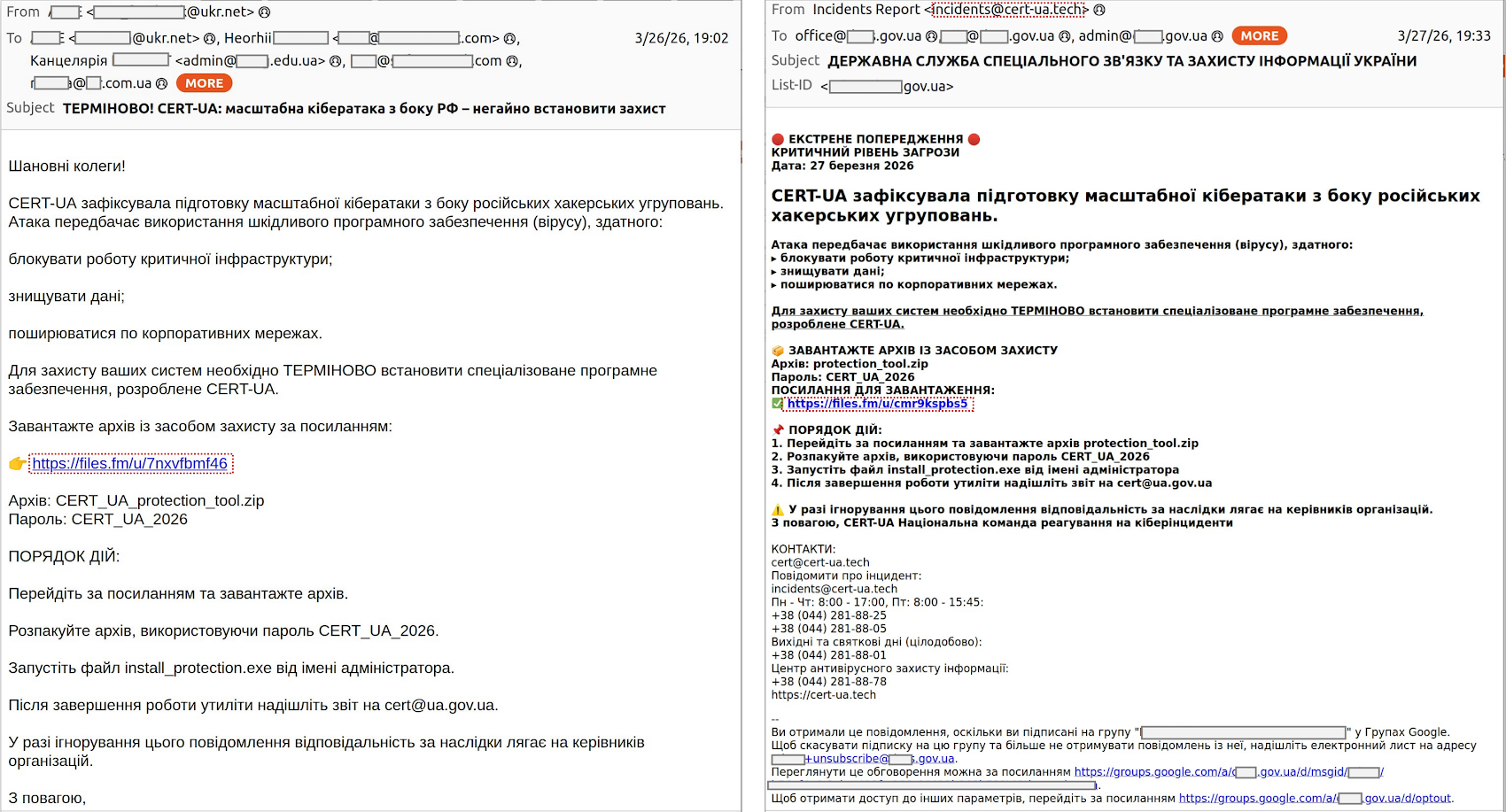
Ukraine's own cybersecurity authority has been weaponized against its citizens. A threat actor tracked as UAC-0255 launched a phishing campaign on March 26-27, impersonating CERT-UA to distribute the AGEWHEEZE remote access trojan across an estimated 1 million ukr.net mailboxes.
The campaign — while largely unsuccessful according to CERT-UA's assessment — represents a sophisticated social engineering attack that exploits institutional trust in Ukraine's primary cybersecurity response team.

How the Attack Works
The attackers sent emails from incidents@cert-ua[.]tech — a convincing lookalike of the legitimate CERT-UA domain. The emails contained a password-protected ZIP file named CERT_UA_protection_tool.zip, hosted on Files.fm, disguised as an official security tool from the agency.
Once extracted and executed, the payload deploys AGEWHEEZE — a Go-based remote access trojan with extensive capabilities:
- Remote command execution
- File system operations (read, write, delete)
- Clipboard modification
- Mouse and keyboard emulation
- Screenshot capture
- Process and service management
The malware communicates with its command-and-control server at 54.36.237[.]92 via WebSocket, making traffic harder to detect with traditional network monitoring.
Who Is Behind It
CERT-UA attributes the campaign to UAC-0255, linked to a cyber-underground operation called Cyber Serp (КИБЕР СЕРП). The group operates via Telegram (channel created November 2025, 700+ subscribers) and claims Ukrainian origins — though this could be a false flag.
Notably, the phishing website's HTML contained a comment: "С Любовью, КИБЕР СЕРП" ("With Love, CYBER SERP"), and showed characteristics of AI-generated content, suggesting the use of large language models in campaign preparation.
Impact Assessment
Despite targeting 1 million mailboxes and claiming over 200,000 compromised devices, CERT-UA assessed the campaign as "largely unsuccessful" — with only a few infected personal devices at educational institutions confirmed. The password protection on the ZIP file and the awareness of Ukrainian users likely limited the blast radius.
Indicators of Compromise
| C2 Server | 54.36.237[.]92 |
| Malicious Domain | cert-ua[.]tech |
| Email Source | incidents@cert-ua[.]tech |
| Payload | CERT_UA_protection_tool.zip |
What to Do
- Verify sender authenticity before opening attachments from security agencies — check the actual domain, not just the display name
- Never open password-protected ZIPs from unsolicited emails
- Block
54.36.237[.]92andcert-ua[.]techat your network perimeter - Monitor for suspicious WebSocket connections to unknown external IPs
- CERT-UA communications are only valid from cert.gov.ua — not any other domain
CyberPeople covers Ukrainian cyber threats daily. Follow us for real-time threat intelligence.





Comments
No comments yet. Be the first to comment!
Leave a Reply
Your email address will not be published.