North Korean hackers exploited Solana durable nonces and social engineering to drain $285M from Drift Protocol — the biggest DeFi hack of 2026.
How North Korean Hackers Stole $285M from Drift Protocol Using Social Engineering and Solana's Own Features
On April 1, 2026, suspected North Korean hackers drained $285 million from Drift Protocol -- the largest decentralized perpetual futures exchange on Solana -- in approximately 12 minutes. The attack did not exploit a smart contract vulnerability. Instead, it weaponized a legitimate Solana blockchain feature called "durable nonces," combined with weeks of social engineering and a manufactured fake token, to bypass every layer of governance security the protocol had in place. It is the largest DeFi exploit of 2026 and the second-largest in Solana's history, behind only the $326 million Wormhole bridge hack of 2022.
This is a cybersecurity story, not just a crypto story. The attack chain -- social engineering, governance manipulation, patient staging, and rapid exfiltration -- mirrors the playbook of nation-state threat actors targeting critical financial infrastructure worldwide. The lessons apply far beyond DeFi.
What Happened: The April Fool's Day Heist
At 16:06 UTC on April 1, 2026, a series of 31 withdrawal transactions began executing against Drift Protocol's vaults. Within 12 minutes, the attacker extracted approximately $285 million in digital assets -- including JLP tokens, USDC, SOL, wrapped Bitcoin (cbBTC, wBTC), and other tokens.
The impact was immediate and devastating:
- Drift's total value locked (TVL) collapsed from approximately $550 million to under $250 million within an hour.
- The DRIFT governance token crashed 40%, dropping from roughly $0.08 to below $0.05.
- Over 20 downstream protocols with exposure to Drift liquidity -- including Prime Numbers Fi, Carrot Protocol, Pyra Protocol, and Piggybank -- were affected. Users across these platforms found their funds inaccessible.
- Drift immediately suspended all deposits and withdrawals, telling users to halt all activity while the team investigated.
The timing was grimly ironic. Many in the crypto community initially dismissed early reports as an April Fool's Day joke. By the time the reality set in, the funds were already being bridged to Ethereum.
The Attack Chain: Social Engineering Meets On-Chain Exploitation
What makes this exploit remarkable -- and alarming -- is that the attacker did not find a bug in Drift's code. The smart contracts functioned exactly as designed. Instead, the adversary spent three weeks methodically compromising the human and governance layers around the protocol.
Phase 1: Infrastructure Staging (March 11)
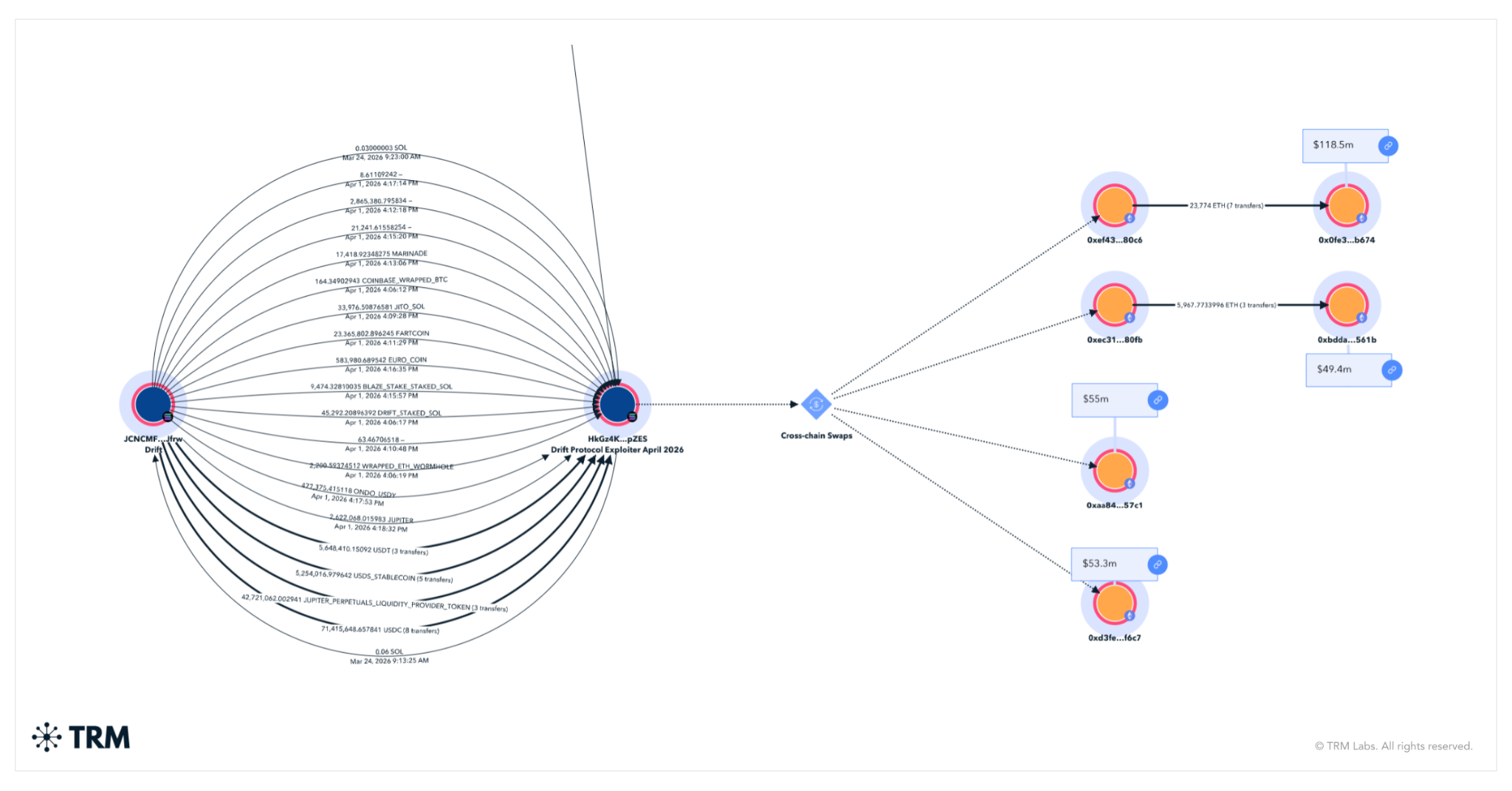
On-chain analysis by TRM Labs traced the attack's origins to March 11, when 10 ETH were withdrawn from Tornado Cash -- the sanctioned cryptocurrency mixer -- to fund initial operations. The funds began moving approximately three hours later, around 09:00 Pyongyang time, a temporal indicator that would later support attribution to North Korean state-sponsored hackers.
Phase 2: Manufacturing a Fake Asset (March 11-23)
The attacker created a fictitious cryptocurrency called CarbonVote Token (CVT), minting approximately 750 million units and controlling over 80% of the supply. They seeded a liquidity pool on Raydium -- a Solana-based decentralized exchange -- with just $500 in initial capital.
Over the following weeks, the attacker engaged in systematic wash trading: repeatedly buying and selling CVT between wallets they controlled to fabricate a legitimate-looking price history near $1 per token. This artificial trading activity generated enough data points that Drift's Switchboard oracle feeds -- the price information sources the protocol relied on -- accepted CVT as a real asset with a credible market value.
This was not a technical oracle exploit. The oracles did what they were designed to do: report observed market prices. The attacker simply manufactured a market that looked real.
Phase 3: Compromising the Multisig (March 23-30)
Between March 23 and March 30, the attacker created four persistent "durable nonce" accounts on Solana. Two of these accounts were linked to Drift's Security Council multisig signers. The other two were controlled directly by the attacker.
Through social engineering -- the specific methods of which remain under investigation -- the attacker obtained pre-signed transaction approvals from Security Council members. These approvals were embedded in durable nonce transactions, meaning they would remain valid indefinitely until the attacker chose to submit them.
The Security Council signers likely believed they were approving routine operations. The durable nonce mechanism ensured their signatures could be held, stored, and deployed at a time and in a context they never intended.
Phase 4: Removing the Last Defense (March 27)
On March 27, Drift migrated its Security Council to a 2-of-5 multisig configuration -- and critically, set the governance timelock to zero seconds.
A timelock is a mandatory delay between when a governance action is approved and when it can be executed. It serves as a critical safety window: if a malicious proposal is approved, the community or security team has time to detect and block it before execution. By setting the timelock to zero, Drift eliminated this last line of defense.
Whether this migration was initiated by the attacker through social engineering, or was a coincidental operational decision that the attacker exploited, remains under investigation. Either way, it converted what would have been a multi-day attack -- detectable during the timelock period -- into an instantaneous one.
Phase 5: Execution (April 1)
With all pieces in place, the attacker executed the final sequence:
- Deposited approximately 785 million fraudulent CVT tokens as collateral into Drift.
- The oracles, relying on the manipulated price history, valued this collateral at hundreds of millions of dollars.
- Withdrawal protections were disabled -- thresholds had been raised to an absurd "$500 trillion," effectively removing all limits.
- Two pre-signed durable nonce transactions, separated by just four Solana block slots, created and approved a malicious admin transfer, then approved and executed it.
- Within minutes, the attacker had full control of Drift's protocol-level permissions.
- 31 withdrawal transactions extracted $285 million in genuine assets against the fake collateral.
The entire execution phase took 12 minutes. The preparation took three weeks.
The Durable Nonce Trick: Turning a Convenience Feature Into a Weapon
Understanding this attack requires understanding how Solana handles transaction validity -- and how durable nonces change the rules.
How Solana Transactions Normally Work
Every Solana transaction includes a "recent blockhash" -- essentially a timestamp proving the transaction was created recently. This blockhash expires after approximately 60 to 90 seconds. If a transaction is not submitted to the network within that window, it becomes invalid and cannot be executed. This expiration mechanism is a safety feature: it prevents old, stale, or potentially compromised transactions from being replayed later.
How Durable Nonces Override This Safety
Durable nonces are a legitimate Solana feature designed for scenarios where transactions need to be prepared in advance -- for example, when multiple parties in different time zones need to sign a multisig transaction. A durable nonce replaces the expiring blockhash with a fixed, one-time code stored in a special on-chain account. This keeps the transaction valid indefinitely until someone chooses to submit it.
The feature exists for good reason. But the Drift exploit revealed its dangerous potential: durable nonces allow an attacker to separate the moment of approval from the moment of execution. A signer can be tricked into approving a transaction today that the attacker executes weeks later, in a completely different context, against a completely different state of the protocol.
This is a fundamental shift in the threat model for any protocol using multisig governance on Solana. Signers can no longer assume that the state of the protocol at the time they sign will be the same state when the transaction executes.
Implications for Multisig Security
The durable nonce attack pattern has broad implications:
- Pre-signed approvals become time bombs. Any durable nonce transaction is a latent authorization that can be deployed at the attacker's convenience.
- Signers cannot verify execution context. The protocol state may change dramatically between signing and execution.
- Standard multisig review processes are insufficient. Reviewing what a transaction does at signing time tells you nothing about what it will do when the attacker decides to submit it.
Every protocol using multisig governance on Solana -- and analogous delayed-execution mechanisms on other chains -- must now account for this attack vector.
DPRK Attribution: North Korea's Expanding Crypto War
TRM Labs, the blockchain intelligence firm, assessed that the Drift exploit was "likely perpetrated by North Korean hackers." While the investigation remains ongoing and formal government attribution has not been issued, multiple lines of evidence support the assessment.
On-Chain Evidence
- Tornado Cash staging: The initial 10 ETH funding came from Tornado Cash, consistent with DPRK operational patterns for obfuscating fund origins.
- Temporal indicators: Key operational activities -- including fund movements and the CarbonVote Token deployment -- occurred around 09:00 Pyongyang time, suggesting coordination from the DPRK timezone.
- Cross-chain laundering speed: Within hours of the theft, over $230 million in USDC was bridged to Ethereum via Circle's Cross-Chain Transfer Protocol (CCTP), then rapidly laundered through Tornado Cash and fragmented across hundreds of Ethereum wallets. TRM described the speed and aggression of the bridging as exceeding "even the Bybit laundering of 2025."
- Infrastructure patterns: The staging infrastructure, wallet creation patterns, and fund movement techniques are consistent with those observed in previous DPRK-attributed operations.
The Broader DPRK Crypto Theft Campaign
North Korea's state-sponsored hacking operations -- commonly attributed to the Lazarus Group and related units -- represent the most prolific nation-state cryptocurrency theft operation in history. The numbers tell a stark story:
- $1.7 billion stolen in 2022
- $1.0 billion stolen in 2023
- $1.3 billion stolen in 2024
- $2.02 billion stolen in 2025, a 51% year-over-year increase
- $6.75+ billion cumulative all-time theft
The February 2025 Bybit exploit -- a $1.5 billion theft from one of the world's largest centralized exchanges -- demonstrated that DPRK operators had graduated from targeting smaller DeFi protocols to striking major financial platforms. The Drift exploit continues this escalation.
In 2026 alone, DPRK-linked actors have been connected to at least three major attacks, including the March 2026 Bitrefill compromise that exposed 18,500 purchase records. Their operational tempo has increased by an estimated 40% compared to 2024, according to open-source intelligence assessments.
These funds are widely believed to finance North Korea's weapons programs, including its nuclear and ballistic missile development. Cryptocurrency theft has become a strategic national revenue stream for the DPRK regime.
Impact on the Solana DeFi Ecosystem
The Drift exploit sent shockwaves far beyond the protocol itself.
Immediate Fallout
Over 20 protocols with direct or indirect exposure to Drift liquidity were affected. Users of downstream platforms like Pyra Protocol remained unable to access their funds as of April 3. DeFi Development Corp., a Nasdaq-listed entity with Solana exposure, was notably unaffected due to its risk framework -- a distinction that highlighted how many other participants lacked similar protections.
Governance and Oracle Trust Crisis
The exploit raised fundamental questions about DeFi governance assumptions:
- Oracle reliability: Drift's oracles performed as designed -- they reported market prices accurately. But they could not distinguish between a legitimate market and a manufactured one. This challenges the foundational assumption that on-chain price data equals market truth.
- Timelock necessity: Drift's decision to set a zero-second timelock on its Security Council migrations removed the one mechanism that could have provided a detection window. The incident has become a textbook case for why timelocks are not optional.
- Multisig assumptions: The 2-of-5 multisig configuration assumed that signers would only approve transactions they fully understood, in contexts they could verify. Durable nonces broke both assumptions.
Comparison to Historical Exploits
The Drift hack joins a growing list of nine-figure DeFi exploits:
| Incident | Year | Amount | Method |
|---|---|---|---|
| Ronin Bridge (Axie) | 2022 | $625M | Validator key compromise |
| Wormhole Bridge | 2022 | $326M | Smart contract vulnerability |
| Bybit | 2025 | $1.5B | Compromised laptop, social engineering |
| Drift Protocol | 2026 | $285M | Social engineering, governance manipulation |
The pattern is clear: the largest exploits increasingly target human and governance layers rather than smart contract code. Social engineering has become the primary attack vector for nation-state-level crypto theft.
What This Means for Ukrainian Organizations
Ukraine's growing fintech and blockchain sector faces direct lessons from the Drift exploit -- and the risks are not theoretical.
Ukraine's Crypto Exposure
Ukraine has been at the forefront of cryptocurrency adoption, ranking consistently among the top countries globally for crypto usage. Ukrainian blockchain projects, DeFi protocols, and fintech companies operate in the same ecosystem targeted by DPRK actors. The country's regulatory framework for virtual assets, adopted under the "Virtual Assets" law, is still maturing, and many Ukrainian crypto startups operate with governance structures similar to those that failed at Drift.
Social Engineering in a Wartime Context
Ukrainian organizations already face elevated social engineering threats due to the ongoing conflict. Russian-linked threat actors routinely target Ukrainian entities with sophisticated phishing and social engineering campaigns. The Drift exploit demonstrates that social engineering targeting multisig signers and governance participants is equally effective against blockchain-native organizations. Ukrainian DeFi projects must treat governance security with the same rigor applied to defending against wartime cyber operations.
Practical Risks for Ukrainian Fintech
- Oracle manipulation: Any Ukrainian DeFi protocol relying on single oracle sources for collateral valuation faces the same vulnerability Drift had. Manufactured tokens with fake price histories can fool technically correct oracle implementations.
- Governance structure weaknesses: Small teams with limited multisig signers, zero or short timelocks, and informal approval processes are common in the Ukrainian startup ecosystem. Each of these was a contributing factor in the Drift exploit.
- Nation-state targeting: DPRK hackers do not discriminate by geography. Any protocol holding significant value is a potential target, regardless of where it is headquartered or where its team operates.
- Regulatory alignment: As Ukraine aligns with EU frameworks including NIS2 and DORA, the Drift incident underscores the need for governance security standards that address blockchain-specific risks -- not just traditional IT infrastructure.
Recovery Efforts and What Happens Next
As of April 3, Drift Protocol escalated its response by sending on-chain messages to four Ethereum wallets holding the bulk of the stolen assets -- approximately 129,000 ETH. The message read: "We are ready to speak," signaling willingness to negotiate. This approach mirrors tactics used by other exploited protocols, though the prospects of recovery from DPRK-linked actors are historically poor.
Key developments in the recovery effort:
- Asset freezing: Drift is cooperating with Circle (USDC issuer), centralized exchanges, and bridge operators to freeze assets where possible. However, over $230 million had already been bridged and laundered through Tornado Cash before freezing could take effect.
- Law enforcement engagement: While details remain limited, Drift has indicated cooperation with law enforcement agencies. Given the DPRK attribution, this will likely involve coordination with US authorities and international sanctions enforcement.
- No reimbursement plan announced: As of April 4, Drift has not published a comprehensive plan for user reimbursement. The status of insurance funds or recovery mechanisms remains unclear.
The broader DeFi community is already responding. Multiple Solana protocols have announced emergency reviews of their governance configurations, timelock settings, and oracle dependencies. The Solana Foundation has not issued a formal statement, but community discussions about durable nonce risk mitigation are active.
Security Recommendations
The Drift Protocol exploit provides concrete, actionable lessons for any organization operating in the blockchain and DeFi space -- and several that apply to traditional cybersecurity as well.
For DeFi Protocols and Blockchain Projects
-
Implement mandatory timelocks on all governance actions. A minimum 24-48 hour timelock on Security Council migrations, admin transfers, and parameter changes would have provided a detection window. Timelocks are not optional -- they are a critical security control.
-
Diversify oracle sources and implement anomaly detection. Relying on a single oracle feed for collateral valuation is insufficient. Protocols should require consensus across multiple independent oracles and implement circuit breakers that pause operations if asset valuations deviate sharply from historical baselines.
-
Restrict or audit durable nonce usage in governance transactions. Any transaction using a durable nonce should trigger enhanced review, including verification that the current protocol state matches the signer's intent. Consider prohibiting durable nonces for high-privilege governance operations entirely.
-
Establish multisig verification protocols. Signers should verify not only what a transaction does, but the context in which it will execute. Implement out-of-band confirmation channels, mandatory cooling-off periods, and real-time alerting for any governance transaction submission.
-
Conduct adversarial governance simulations. Red-team your governance processes with the same rigor applied to smart contract audits. Test whether social engineering of signers could lead to unauthorized actions.
For Organizations and Security Teams
-
Treat governance security as operational security. The Drift exploit was not a code vulnerability -- it was a governance compromise. Security programs must extend beyond code audits to cover human processes, approval workflows, and administrative access patterns.
-
Monitor for social engineering targeting key personnel. Multisig signers, treasury managers, and governance participants are high-value social engineering targets. Implement awareness training and verification protocols specifically for these roles.
-
Maintain incident response plans for DeFi exposure. Organizations with treasury or operational exposure to DeFi protocols should have playbooks for rapid response to exploit events, including asset withdrawal procedures, communication templates, and counterparty risk assessment.
For the Industry
-
Develop standards for governance security in DeFi. The recurring pattern of governance-layer exploits demands industry-wide standards for timelock minimums, multisig configurations, oracle diversity requirements, and admin privilege restrictions.
-
Share threat intelligence on nation-state DeFi targeting. The DPRK threat to DeFi is systemic. Protocols, security firms, and regulators must share intelligence on attack patterns, staging indicators, and attribution findings to enable collective defense.
The Drift Protocol exploit is a reminder that in cybersecurity, the most dangerous vulnerabilities are often not in the code -- they are in the processes, the people, and the assumptions we fail to question. For Ukrainian organizations operating at the intersection of technology, finance, and national security, these lessons are not abstract. They are operational.
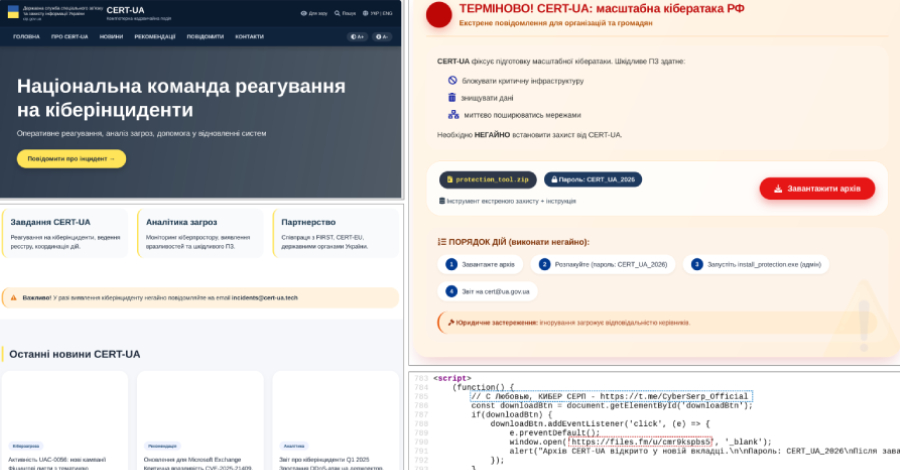
Related reading on CyberPeople: - Attackers Impersonated CERT-UA to Deliver AGEWHEEZE Malware to 1 Million Ukrainian Mailboxes - Operation NoVoice: The Android Rootkit That Survives Factory Reset
Sources: - TRM Labs: North Korean Hackers Attack Drift Protocol In $285 Million Heist - CoinDesk: How a Solana Feature Designed for Convenience Let an Attacker Drain $270 Million from Drift - CryptoTimes: $285M Gone in 12 Minutes - Bitcoin.com: Drift Protocol Hack 2026 -- What Happened, Who Lost Money, and What's Next - CCN: Drift Protocol Hit by $285M Exploit - DL News: Solana-based Drift Protocol confirms it's under attack - FXStreet: Solana DEX Drift Protocol suffers $280M+ attack




Comments
No comments yet. Be the first to comment!
Leave a Reply
Your email address will not be published.