Is your email in a data breach?
Check breaches & infostealer malware in 10 seconds. Free.
Your email is never stored. Checked: 123
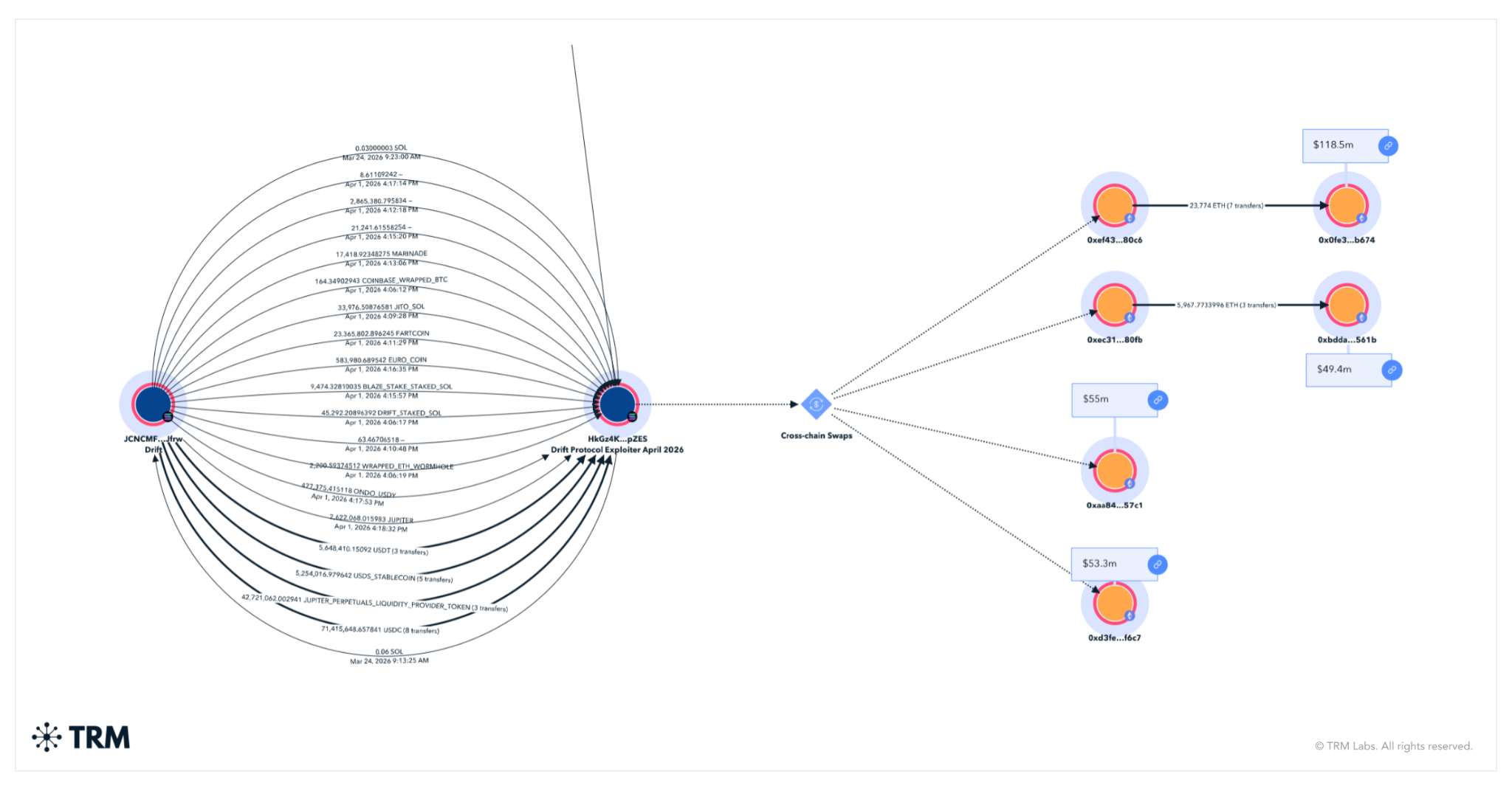
How North Korean Hackers Stole $285M from Drift Protocol Using Social Engineering and Solana's Own Features
North Korean hackers exploited Solana durable nonces and social engineering to drain $285M from Drift Protocol in 12 min...
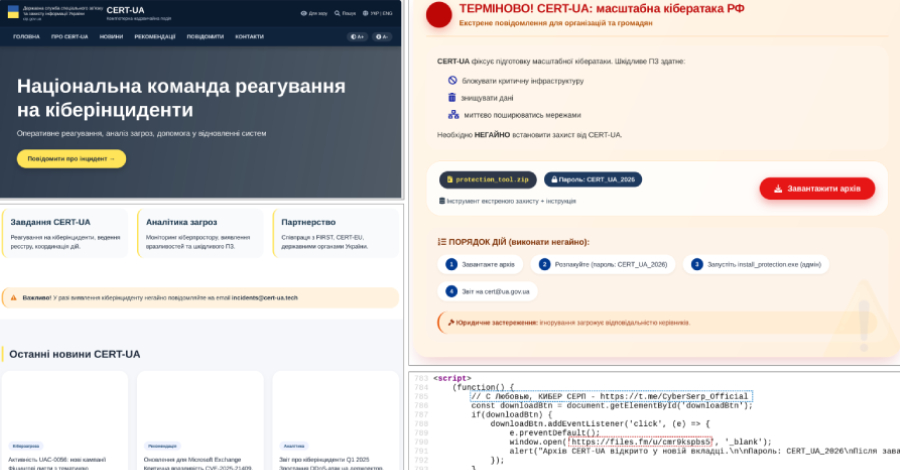
CERT-UA Impersonated: AGEWHEEZE Malware Campaign Targets Ukrainian Organizations
A phishing campaign impersonating Ukraine's Computer Emergency Response Team (CERT-UA) attempted to distribute the AGEWH...

Cybersec Europe 2026: Where European Cybersecurity Comes Together
Cybersec Europe returns to Brussels Expo on May 20-21, 2026 with live hacking demos, EU policy debates, Cybersec Europe...

KITE 2026 — Ukraine's Premier OSINT & Cybersecurity Conference
The second annual KITE (Kyiv Intelligence & Technology Exchange) brings together intelligence, OSINT, and cybersecurity...

SANS AI Cybersecurity Summit 2026: Where AI Meets Cyber Defence
The SANS AI Cybersecurity Summit brings together cybersecurity professionals, AI/ML experts, and thought leaders at the...
CYBERUK 2026 — The Next Decade: Accelerating Our Cyber Defence
The UK's National Cyber Security Centre (NCSC) brings its flagship conference back to Glasgow's SEC from April 21-23, 20...

Telegram C2 Is Breaking
A few years ago, Telegram became an almost universal solution for cybercriminals. It covered several needs at once: a co...

Anthropic Publishes Report on Risks of the Claude Opus 4.6 Model
Anthropic has released a technical report assessing risks associated with its large language model, Claude Opus 4.6. The...